Guide - Cyber and Digital Risk Metrics for Boards
What Good Cyber and Digital Oversight Looks Like
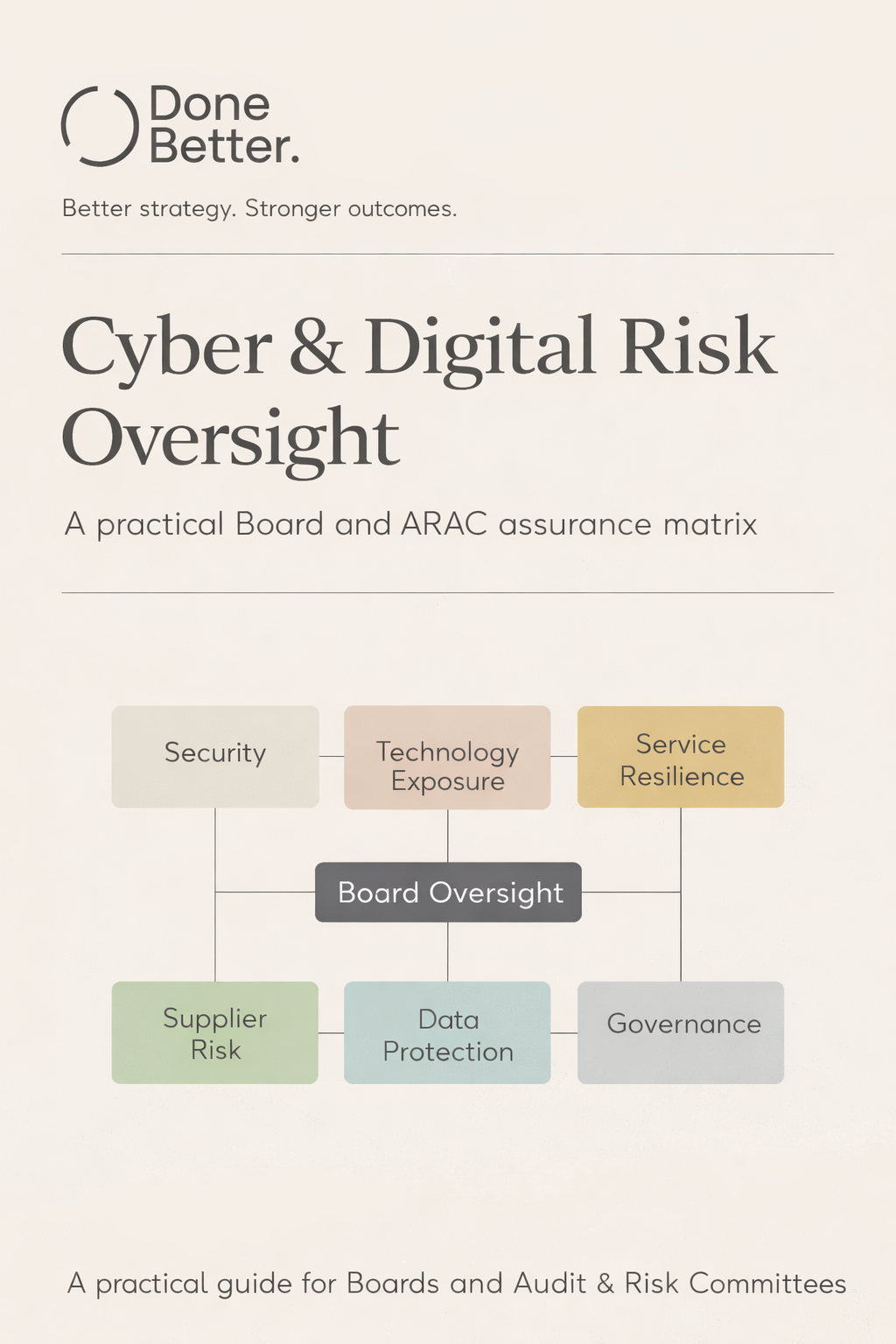
Boards are increasingly asking whether they have the right metrics in place to know that cyber and digital risk is being governed effectively.
Most Boards understand that they should not be reviewing technical dashboards or operational detail. What they do need is visibility across the strategic risks created by technology. That means seeing indicators that reflect harm, exposure, resilience, supplier dependency and governance discipline.
The challenge is not producing more reporting. It is selecting measures that genuinely reflect enterprise risk rather than operational activity.
“Have we got the right metrics to know we are governing cyber and digital risk effectively?”
Here is a practical example of a set of metrics grouped by strategic digital risk that you can implement in your organisation
Risk 1 - Security Incidents affecting Systems and Data
Metric: Serious security incidents causing business impact
Definition: Any event that compromises the confidentiality, integrity or availability of systems or data and resulted in material impact to business operations, financial loss, regulatory notification or executive escalation. This includes malicious attacks, accidental data loss, insider misuse, system misconfiguration or technology failure.
Why it matters: This confirms whether cyber or digital risk has already crystallised into real organisational harm.
Metric: Total security incidents requiring formal investigation, shown as a trend
Definition: Events where there was credible risk to systems or data requiring structured investigation.
Why it matters: The direction of travel provides insight into whether exposure is increasing or detection capability is improving.
Risk 2 - Technology Exposure and Compliance
Metric: Serious security weaknesses not fixed within 14 days where an update is available
Definition: Important security updates that have not been applied within recognised timeframes.
Why it matters: This reflects baseline security discipline. Persistent delay increases forward exposure.
Metric: Serious security weaknesses without protective measures
Definition: Known weaknesses where no vendor update exists and no alternative mitigation has been implemented.
Why it matters: This highlights unmanaged exposure rather than theoretical risk.
Metric: Digital systems, applications or platforms not supported by the vendor
Definition: Technology in use that no longer receives vendor security updates.
Why it matters: Unsupported systems represent structural exposure and frequently sit at the root of major incidents.
Risk 3 - Digital Service Resilience
Metric: Service disruptions exceeding agreed tolerance
Definition: Digital outages lasting longer than the Board-approved duration for critical systems.
Why it matters: This connects digital risk directly to business operations and service delivery.
Metric: Critical digital services not tested for recovery within the required period
Definition: Important systems supporting business operations and service delivery that have not had their recovery arrangements recently validated through structured testing.
Why it matters: Recovery capability should be evidenced, not assumed.
Risk 4 - Supplier and Supply Chain
Metric: Serious supplier-related service or data incidents
Definition: Material disruption or exposure attributable to suppliers whose failure or compromise would significantly affect business operations, service delivery or sensitive data.
Why it matters: Supply chain exposure is now one of the most common sources of digital harm.
Metric: Critical suppliers without up-to-date security and resilience assurance
Definition: Suppliers (both IT and non-IT) essential to business operations and service delivery that have not been reviewed within the agreed governance cycle.
Why it matters: If key suppliers are not periodically assured, the Board cannot be confident that third-party exposure is understood.
Metric: Suppliers handling sensitive data without an appropriate data protection agreement
Definition: Third-party processors of personal data without formal contractual safeguards in place.
Why it matters: This represents direct statutory and regulatory exposure.
Risk 5 - Data Protection and Privacy Risk
Metric: Reportable personal data breaches
Definition: Personal data breaches that met the legal threshold for regulatory notification.
Why it matters: This indicates crystallised privacy harm and regulatory exposure.
Metric: High-risk processing introduced without a required impact assessment
Definition: Significant personal data processing activities started without a Data Protection Impact Assessment where legally required.
Why it matters: This tests statutory accountability and governance discipline.
Metric: Data protection training completion below agreed minimum
Definition: Percentage of staff completing mandatory data protection training falling below the agreed baseline.
Why it matters: Behavioural risk remains one of the most common contributors to data incidents.
Risk 6 - Digital Governance and Assurance
Metric: Cyber security training completion below agreed minimum
Definition: Percentage of staff completing mandatory cyber awareness training falling below the agreed baseline.
Why it matters: This addresses human attack surface risk.
Metric: Significant digital control weaknesses identified by audit
Definition: Material weaknesses in digital controls identified through internal or external review.
Why it matters: Independent assurance provides an objective view of control effectiveness.
Significant digital control weaknesses not fixed by the agreed deadline
Definition: Material weaknesses that remain overdue beyond agreed remediation timeframes.
Why it matters: This tests governance follow-through and remediation discipline.
If we could only pick three?
Whilst we’d strongly recommend you have the full set of metrics, if an Audit and Risk Committee wanted to reduce oversight to a minimum viable set, the three measures that provide the broadest and most meaningful coverage would be:
1. Serious security incidents causing business impact
This confirms whether cyber or digital risk has already crystallised into material harm affecting business operations, finances or regulatory standing.
2. Serious security weaknesses not fixed within 14 days
This indicates whether baseline security discipline is being maintained and whether forward exposure is increasing.
3. Critical suppliers without up-to-date security and resilience assurance
This highlights external dependency risk and whether supplier exposure is being actively governed
Download the full matrix
The overview above is designed for clarity.
A detailed version of the full matrix, including governance questions, illustrative tolerances and linked compliance references, is available as a downloadable guide. It can be used to review your current reporting or as a starting point for designing a Board dashboard aligned to your organisation’s risk appetite and maturity.
Every organisation’s digital estate and governance model is different.
If you would like support reviewing your current reporting, defining tolerances or designing a Board-ready cyber and digital assurance model that fits your context, feel free to get in touch.
Effective oversight is not about more metrics. It is about the right ones.